NIS2, which is expected to be adopted by 17 October 2024, is a directive aimed at developing, standardizing and integrating cybersecurity capabilities in all Member States of the European Union.
It aims first and foremost to define guidelines on national strategies on Cybersecurity, through the creation of a network of competent authorities that carry out crisis management activities, act as contact points and manage Cybersecurity Incident Response Teams (CSIRTs).
Another important issue, with a direct impact on the market, concerns the definition of cybersecurity risk management measures and incident reporting obligations, as well as fines in the event of non-compliance or failure to report. The number of organizations involved, compared to the previous NIS directive, has been expanded considerably, and is defined on the basis of belonging to critical sectors and the size of the companies.
The sectors defined as highly critical are:
- Energy
- Transport
- Banking
- Financial market infrastructures
- Health
- Drinking water
- Waste water
- Digital infrastructures
- ICT service management (business-to-business)
- Public administration
- Space
In addition to these, there are further critical sectors:
- Postal and courier services
- Waste management
- Manufacture, production and distribution of chemicals
- Production, processing and distribution of food
- Manufacturing (of medical devices, electronics, machinery, transport equipment)
- Digital providers
- Research
The Directive defines essential entities that include, among others, large companies belonging to highly critical sectors, providers of certain network and telecommunications services and any entity that a Member State identifies as operator of essential services.
The audience widens if we consider the important entities: these include companies, even small ones, operating in all critical sectors, or in any case recognized as important by the Member States due to the potential impact of a disruption of their services.
The essential and important entities must substantially apply the same measures, while the differences between the two concern the monitoring of application and the extent of fines in case of non-compliance.
It is therefore clear that NIS2 is aimed directly at a large chunk of the European economic fabric, and if we look at the possible ramifications we find that the list expands further: essential and important entities have, in fact, the obligation to verify that their suppliers also adopt adequate and proportionate Cybersecurity measures.

What are the measures that essential and important entities must apply?
The NIS2 Directive provides some guidelines on the management of Cybersecurity risks, which are concentrated in Article 21, paragraph 2, and are:
(a) policies on risk analysis and information system security;
(b) incident handling;
(c) business continuity, such as backup management and disaster recovery, and crisis management;
(d) supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers;
(e) security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure;
(f) policies and procedures to assess the effectiveness of cybersecurity risk-management measures;
(g) basic cyber hygiene practices and cybersecurity training;
(h) policies and procedures regarding the use of cryptography and, where appropriate, encryption;
(i) human resources security, access control policies and asset management;
(j) the use of multi-factor authentication or continuous authentication solutions, secured voice, video and text communications and secured emergency communication systems within the entity, where appropriate.
Each of these points can be applied through organizational and technological measures, finding a mapping with the different solutions on the market.
ZAIUX Evo’s support for compliance
We see, in particular, that point (f) focuses on validating the effectiveness of the security measures adopted, testing one’s defensive posture.
A very effective methodology, from this point of view, consists in simulating cyber attacks on infrastructures, so as to bring out any critical issues through field tests.
In this, organizations affected by NIS2 can find a valuable ally in ZAIUX® Evo, Pikered’s Breach & Attack Simulation (BAS) solution.
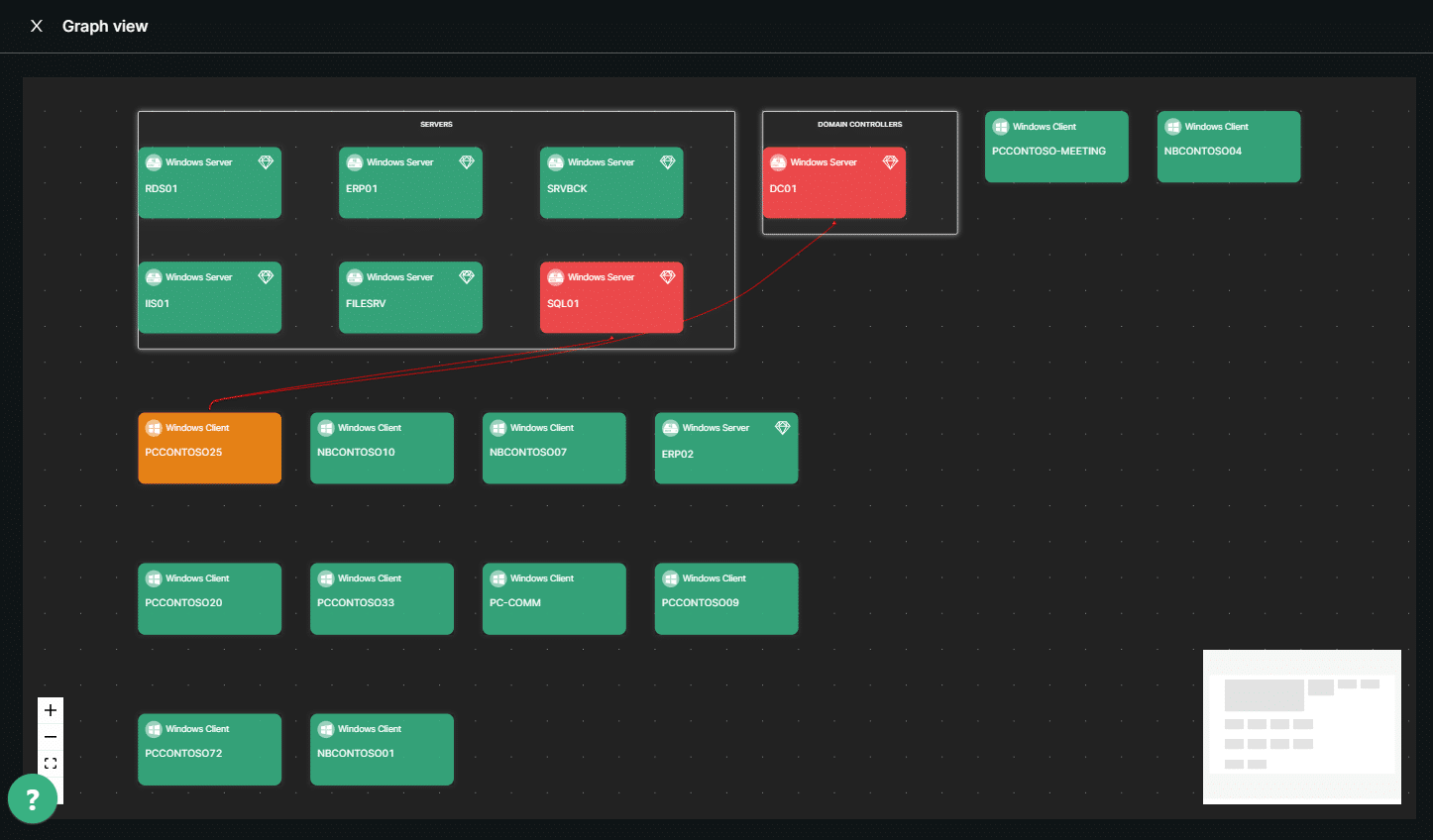
Thanks to the ZAIUX Evo platform, it is possible to emulate an attack scenario in which a malicious actor has gained initial access to an MS Active Directory infrastructure, for example through a phishing campaign. The software is therefore able to exploit advanced attack vectors and try to move within the network and increase its privileges, while performing techniques that simulate the exfiltration of information and the controlled deployment of a Ransomware; all through a malware commanded by an external Command and Control server, as in a real attack. This makes it possible to assess the real ability of the solutions and defense teams to detect and block threats, verifying the adequacy of the Cybersecurity management measures.
Thanks to its simplicity and scalability, ZAIUX Evo is the ideal BAS solution for MSPs who want to help their customers achieve NIS2 compliance. The management is in fact completely centralized in a single Web interface, and the configuration and execution of a BAS requires neither Cybersecurity skills nor deployment of any kind, since the activity is started as a malware infection, with the simple launch of an executable.
At the end of each BAS, ZAIUX Evo generates a clear and concise report, which can be used to guide Remediation actions: this is also thanks to the lack of false positives, since all techniques are carried out concretely, in realistic attack scenarios.
In addition, the business model of ZAIUX Evo makes it easily adaptable to different needs. In fact, deployment takes place by means of Execution Tokens, each of which allows a complete BAS on an Active Directory domain. This makes it possible to size the frequency of simulations based on the speed of application of mitigations between one BAS and another, thus also adapting to different scenarios of criticality and spending possibilities of the organizations involved in the imminent application of NIS2, allowing them to implement an effective strategy for evaluating the effectiveness of the adopted Cybersecurity technologies.
